WHAT'S NEW
ACCESSORIES
Africa Lost $3.5 Billion to Cybercrime in 2017
What is SIEM ?
WINDOWS PHONE
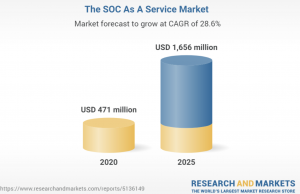
SOC as a Service Market by Component, Service Type (Prevention, Detection,...
LATEST ARTICLES
What is Cyber Crime
What is Cyber Crime ? The term ‘cyber crime’ refers to any unlawful activity involving a computer Network or a connected device of...
Shocking 12 Recent Major Cyber Attacks 2026 That Are Reshaping Global Security
The year 2026 has already witnessed an alarming rise in cybercrime activity worldwide. From large-scale ransomware incidents to sophisticated nation-state espionage campaigns, the recent...
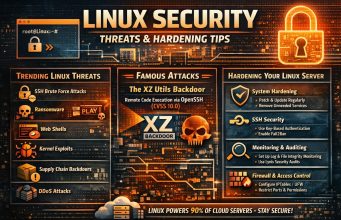
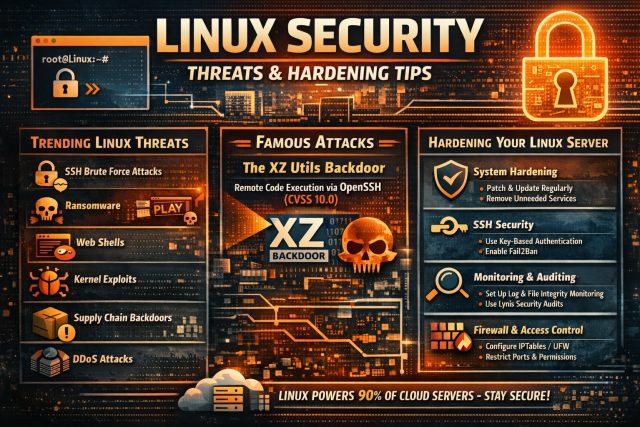
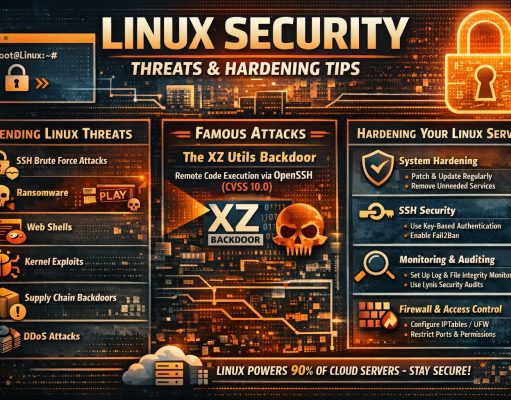
Linux Security in 2026: Threat Landscape, Trending Attacks, and How to Harden Your Servers
Linux underpins cloud infrastructure, containers, edge devices, and supercomputers — and while it’s long been regarded as a secure platform, attackers are increasingly focusing...
Safeguarding the Backbone of the Global Economy: OT/ICS Security in the Oil and Gas Industry
The oil and gas industry is an essential pillar of the global economy, enabling energy production, transportation, and storage that fuel every aspect of...
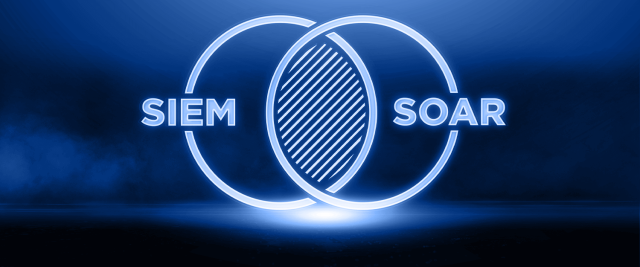
Detailed Guide to SOAR and SIEM
What Is SOAR? SOAR stands for Security Orchestration, Automation, and Response. It’s a cybersecurity tool designed to simplify and enhance the efficiency of IT teams...
What is a cyberattack?
What is a cyberattack? Cyberattacks aim to damage or gain control or access to important documents and systems within a business or personal computer network. Cyberattacks...
What is SIEM ?
Security information and event management, SIEM for short, is a solution that helps organizations detect, analyze, and respond to security threats before they harm...
Cyber Security Operation Center Guidelines for best practices SOC Design
Cyber Security is become most needed services for all business and industries in 2024. Every business is concerned about Cyber Security. Security operations (SecOps)...
HOW TO BECOME CERTIFIED LEAD IMPLEMENTER – ISO 27001
ABOUT CERTIFIED LEAD IMPLEMENTER TRAINING AND EXAMINATION FOR INFORMATION SECURITY MANAGEMENT SYSTEM ISO / IEC 27001 Learn and get certified as a professional in implementation...
YouTube disrupted in Pakistan as former PM Imran Khan streams speech
NetBlocks metrics confirm the disruption of YouTube on multiple internet providers in Pakistan on Sunday 21 August 2022. The disruption comes as former Prime...
Recommendations for Parents about Cyber Bullying
Here are some dedicated tips for keeping younger children safe online. One of these training tips goes into the risks of young children on...




![CRIMEWATCH 2015 EPISODE 10 [Part 1] – 2013 Singapore Cyber Attacks hacked](https://www.cybercrimeswatch.com/wp-content/uploads/2016/06/hacked.png)